In today’s digital-first economy, data is the lifeblood of nearly every small and medium-sized busin...


In today’s digital-first economy, data is the lifeblood of nearly every small and medium-sized busin...

Securing Laptops, Phones, and Everything In Between Use of laptops, tablets, and mobile phones for b...

What Is Pen Testing and Why You Can’t Ignore It Penetration testing, also called Pen testing, is a s...

10 Points CCPA Compliance Checklist: Ensuring Data Protection and Privacy Non-compliance can lead yo...
Anatomy of Social Engineering on LinkedIn This message is an actual example of a social engineering ...

There is no other way to say it, compliance is here to stay. It used to only apply to select industr...

The advancement in technology is increasing the multitude of cyber threats not just for individuals ...
Data security is a structural approach to preventing unauthorized access, change, disclosure, and de...

How Cybersecurity Enhances the Value of Your Business for Potential Investors In today's digital mar...

In the evolving digital landscape, the size of a business is no longer a metric to judge the potenti...

As per one of the recent researches by a prominent consulting practice, cyberattacks have increased ...

“Brute force intrusions, default credentials, and other unsophisticated attack methods were noted by...

“Healthcare providers, health plans, and connected entities across the U.S. would be subjected to mi...
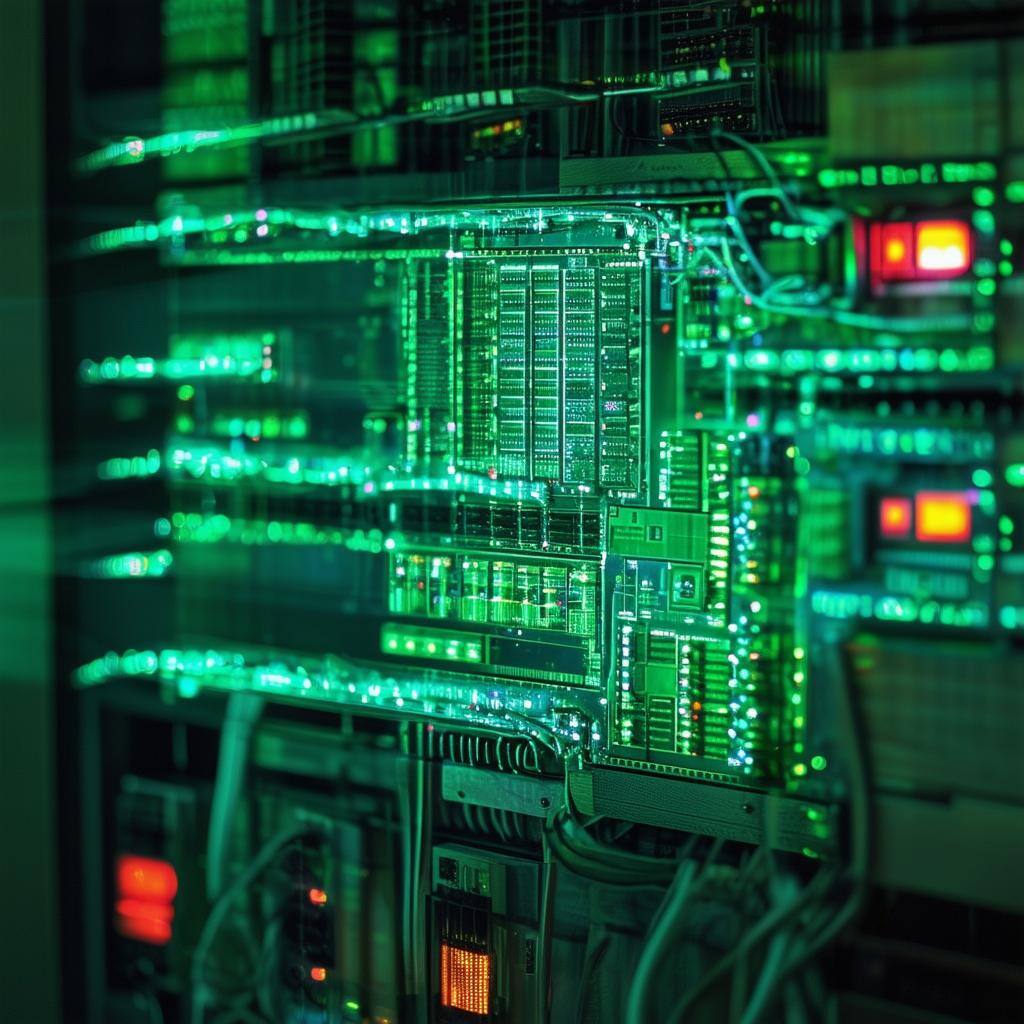
Cisco’s Talos reported critical and high-severity flaws in OpenPLC that could lead to DoS condition ...

In a major policy reversal, the popular messaging app Telegram has announced it will give users’ IP ...